Secured Microcontroller Hardware Security
Secured Microcontroller Hardware Security
When the existence of a backdoor in highly secure Microcontrollers was discovered in the form of secret test/debug interface capable of overriding chip security policy, it raised a lot of questions about Secured Microcontroller Hardware Security of modern ICs.
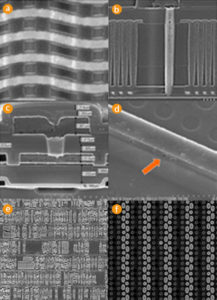
Recently demonstrated method for the direct imaging of EEPROM and Flash memory contents using easily accessible Scanning Electron Microscopes (SEM) challenges the security of embedded storage. This is because non-volatile memory was always considered as being highly secure against most invasive MCU crack due to very small electrical charge accumulated beneath very thin barrier that cannot survive de-processing. Now the obvious question is: What could be the next in ground IC breaking and disturbing attack on hardware security?
In many cases new MCU attacks were far from being something absolutely new. For example, structural analysis for impurities using chemical methods were known for decades and actively used in Failure Analysis. The fact that switching of each individual transistor contributes to the overall power consumption of the circuit was not new and was actively used by semiconductors development tools to predict power consumption and overheating. Even the photon emission was known, but was too expensive as common attack technology.
The fact that photons can interact with transistors was known since the development of transistors and was even used for communication. The ability of electron beam to detect buried charge was also known, but only with the development of more sensitive microscopes became practical to use. The main message of this paper is if the vast majority of IC code extraction are based on already known facts, there must be a way to predict such attacks and develop mitigation techniques well ahead of the active use by attackers.