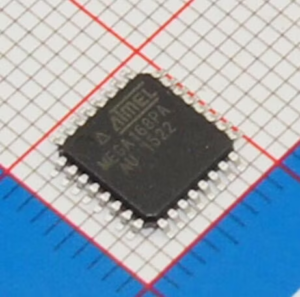
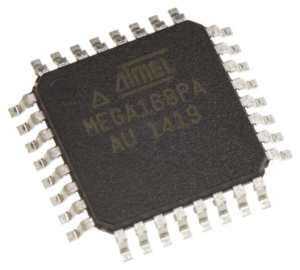
Recover IC ATMEGA168PA Program
Recover IC ATMEGA168PA Program
Recovering IC ATMEGA168PA program often requires expertise in cracking or decoding its encrypted firmware to access the locked content stored within this secured microcontroller. The ATMEGA168PA, a protective microcomputer, is designed to safeguard its EEPROM memory, firmware, and binary data, ensuring that its program and source code remain protected from unauthorized access. Reverse engineering plays a pivotal role in unlocking its protective mechanisms, allowing professionals to analyze and extract the embedded software.
Recovering IC ATMEGA168PA program often requires expertise in cracking or decoding its encrypted firmware to access the locked content stored within this secured microcontroller. The ATMEGA168PA, a protective microcomputer, is designed to safeguard its EEPROM memory, firmware, and binary data, ensuring that its program and source code remain protected from unauthorized access. Reverse engineering plays a pivotal role in unlocking its protective mechanisms, allowing professionals to analyze and extract the embedded software.
The process typically involves identifying the microcontroller’s encryption layers and using specialized tools to break or bypass its security measures. By decoding the binary or heximal structure of the program, the locked firmware can be accessed and restored for authorized purposes. This may include cloning the firmware to replicate hardware, creating backups, or performing system diagnostics to resolve operational issues.
Unlocking and recovering the program from the IC ATMEGA168PA enables developers to restore lost or corrupted source code, ensuring continued functionality of critical systems. Cloning the secured microprocessor can also provide a reliable backup for future use, safeguarding against potential data loss.

восстановление программы IC ATmega168PA часто требует экспертных знаний по взлому или декодированию ее зашифрованной прошивки для доступа к заблокированному содержимому, хранящемуся в этом защищенном микроконтроллере ATmega168PA. ATMEGA168PA, защитный микрокомпьютер ATmega168PA, разработан для защиты своей памяти EEPROM, прошивки и двоичных данных, гарантируя, что его программа и исходный код остаются защищенными от несанкционированного доступа. Обратное проектирование играет ключевую роль в разблокировке его защитных механизмов, позволяя профессионалам анализировать и извлекать встроенное программное обеспечение.
However, breaking or cracking the protective measures of such an MCU must adhere to ethical and legal guidelines. Unauthorized recovery or cloning of its program could infringe on intellectual property rights, emphasizing the need for responsible practices.
The lowest addresses in the program memory space are by default defined as the Reset and Interrupt Vectors. The complete list of vectors is shown in ”Interrupts” on page 56. The list also determines the priority levels of the different interrupts. The lower the address the higher is the priority level.
RESET has the highest priority, and next is INT0 – the External Interrupt Request; The Interrupt Vectors can be moved to the start of the Boot Flash section by setting the IVSEL bit in the MCU Control Register (MCUCR). Refer to ”Interrupts” on page 56 for more information.
The Reset Vector can also be moved to the start of the Boot Flash section by programming the BOOTRST Fuse, see ”Boot Loader Support – Read-While-Write Self-Programming, ATmega168PA
When an interrupt occurs, the Global Interrupt Enable I-bit is cleared and all interrupts are disabled. The user software can write logic one to the I-bit to enable nested interrupts after breaking off atmega168a secured microcontroller fuse bit. All enabled interrupts can then interrupt the current interrupt routine.
recuperar o programa IC ATmega168PA geralmente requer experiência em quebrar ou decodificar seu firmware criptografado para acessar o conteúdo bloqueado armazenado dentro deste microcontrolador ATmega168PA protegido. O ATMEGA168PA, um microcomputador ATmega168PA protetor, é projetado para proteger sua memória EEPROM, firmware e dados binários, garantindo que seu programa e código-fonte permaneçam protegidos contra acesso não autorizado. A engenharia reversa desempenha um papel fundamental no desbloqueio de seus mecanismos de proteção, permitindo que profissionais analisem e extraiam o software incorporado.
The I-bit is automatically set when a Return from Interrupt instruction – RETI – is executed. There are basically two types of interrupts. The first type is triggered by an event that sets the Interrupt Flag. For these interrupts, the Program Counter is vectored to the actual Interrupt Vector in order to execute the interrupt handling routine, and hardware clears the corresponding Interrupt Flag by Crack MCU Flash.
Interrupt Flags can also be cleared by writing a logic one to the flag bit position(s) to be cleared. If an interrupt condition occurs while the corresponding interrupt enable bit is cleared, the Interrupt Flag will be set and remembered until the interrupt is enabled, or the flag is cleared by software.
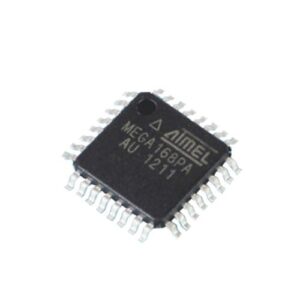
attack atmega168pa microcontroller protection and readout heximal file from atmega168pa flash memory and eeprom memory
Similarly, if one or more interrupt conditions occur while the Global Interrupt Enable bit is cleared, the corresponding Interrupt Flag(s) will be set and remembered until the Global Interrupt Enable bit is set, and will then be executed by order of priority.
The second type of interrupts will trigger as long as the interrupt condition is present. These interrupts do not necessarily have Interrupt Flags. If the interrupt condition disappears before the interrupt is enabled, the interrupt will not be triggered.
When the AVR exits from an interrupt, it will always return to the main program and execute one more instruction before any pending interrupt is served. Note that the Status Register is not automatically stored when entering an interrupt routine, nor restored when returning from an interrupt routine to replicate atmega168p avr mcu flash memory content file. This must be handled by software. When using the CLI instruction to disable interrupts, the interrupts will be immediately disabled. No interrupt will be executed after the CLI instruction, even if it occurs simultaneously with the CLI instruction. The following example shows how this can be used to avoid interrupts during the timed EEPROM write sequence.
غالبًا ما يتطلب استرداد برنامج IC ATmega168PA خبرة في كسر أو فك تشفير البرامج الثابتة المشفرة للوصول إلى المحتوى المقفل المخزن داخل متحكم ATmega168PA الآمن هذا. تم تصميم ATMEGA168PA، وهو كمبيوتر ATmega168PA وقائي، لحماية ذاكرة EEPROM والبرامج الثابتة والبيانات الثنائية، مما يضمن حماية برنامجه ورمزه المصدر من الوصول غير المصرح به. تلعب الهندسة العكسية دورًا محوريًا في فتح آليات الحماية الخاصة به، مما يسمح للمحترفين بتحليل واستخراج البرامج المضمنة.