Recover Chip PIC12CE518 Binary
Recover Chip PIC12CE518 Binary
The PIC12CE518 microcontroller, widely used in embedded systems, stores critical firmware in its internal memory. Sometimes, due to corruption, loss of access, or the need for system modifications, there may be a need to recover or restore the chip’s binary. At [Your Company Name], we specialize in recovering the PIC12CE518 binary using advanced techniques to decode, decrypt, and reverse engineer the firmware, providing you with full access to your system’s data.
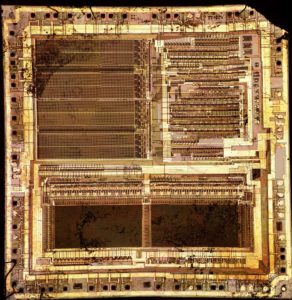
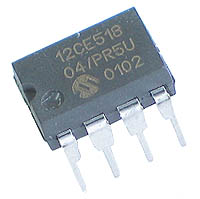
![Der Mikrocontroller PIC12CE518, der in eingebetteten Systemen weit verbreitet ist, speichert kritische Firmware in seinem internen Speicher. Manchmal kann es aufgrund von Beschädigungen, Zugriffsverlusten oder der Notwendigkeit von Systemänderungen erforderlich sein, die Binärdatei des Chips wiederherzustellen oder wiederherzustellen. Bei [Name Ihres Unternehmens] sind wir auf die Wiederherstellung der Binärdatei des PIC12CE518 spezialisiert und verwenden fortschrittliche Techniken zum Dekodieren, Entschlüsseln und Reverse Engineering der Firmware, sodass Sie vollen Zugriff auf die Daten Ihres Systems erhalten.](https://www.ic-crack.com/wp-content/uploads/2015/04/dscf4968_cropped-296x300.jpg)
Der Mikrocontroller PIC12CE518, der in eingebetteten Systemen weit verbreitet ist, speichert kritische Firmware in seinem internen Speicher. Manchmal kann es aufgrund von Beschädigungen, Zugriffsverlusten oder der Notwendigkeit von Systemänderungen erforderlich sein, die Binärdatei des Chips wiederherzustellen oder wiederherzustellen. Bei [Name Ihres Unternehmens] sind wir auf die Wiederherstellung der Binärdatei des PIC12CE518 spezialisiert und verwenden fortschrittliche Techniken zum Dekodieren, Entschlüsseln und Reverse Engineering der Firmware, sodass Sie vollen Zugriff auf die Daten Ihres Systems erhalten.
Our team of experts uses a series of sophisticated tools and methods to crack the chip’s security and break any obfuscation techniques protecting the firmware. We can reverse engineer the binary code from the PIC12CE518, even if the data has been intentionally encrypted or encoded. This process enables us to uncover valuable insights into how the system functions, detect potential vulnerabilities, and assist with debugging or customizing the firmware for your specific needs.

Нашият екип от експерти използва серия от усъвършенствани инструменти и методи, за да пробие сигурността на чипа и да разбие всички техники за обфускация, защитаващи фърмуера. Можем да проектираме обратно двоичния код от PIC12CE518, дори ако данните са умишлено криптирани или кодирани. Този процес ни позволява да разкрием ценна информация за това как функционира системата, да открием потенциални уязвимости и да помогнем при отстраняване на грешки или персонализиране на фърмуера за вашите специфични нужди.
Whether you need to attack a particular piece of firmware to extract sensitive information, hack into a locked system, or restore lost data, our services are tailored to handle complex challenges. We employ state-of-the-art methods to decrypt any protection schemes, ensuring a secure, efficient recovery process.
With our knowledge in embedded systems and microcontroller architectures, we can assist with various tasks, from decoding encrypted firmware to extracting the binary for modifications or audits. We understand the importance of confidentiality, security, and precision in these delicate processes.
Cho dù bạn cần tấn công một phần chương trình cơ sở cụ thể để trích xuất thông tin nhạy cảm, hack vào hệ thống bị khóa hoặc khôi phục dữ liệu đã mất, các dịch vụ của chúng tôi đều được thiết kế riêng để xử lý các thách thức phức tạp. Chúng tôi sử dụng các phương pháp tiên tiến nhất để giải mã mọi chương trình bảo vệ, đảm bảo quy trình khôi phục an toàn và hiệu quả.
Với kiến thức về hệ thống nhúng và kiến trúc vi điều khiển, chúng tôi có thể hỗ trợ nhiều nhiệm vụ khác nhau, từ giải mã chương trình cơ sở được mã hóa đến trích xuất nhị phân để sửa đổi hoặc kiểm tra. Chúng tôi hiểu tầm quan trọng của tính bảo mật, an ninh và độ chính xác trong các quy trình tinh vi này.
As a program instruction is executed, the Program Counter (PC) will contain the address of the next program instruction to be executed by Recover Chip PIC12CE518 Binary. The PC value is increased by one every instruction cycle, unless an instruction changes the PC. For a GOTO instruction, bits 8:0 of the PC are provided by the GOTO instruction word. The PC Latch (PCL) is mapped to PC<7:0>. Bit 5 of the STATUS register provides page information to bit 9 of the PC (Figure 4- 8).
For a CALL instruction, or any instruction where the PCL is the destination, bits 7:0 of the PC again are provided by the instruction word. However, PC<8> does not come from the instruction word, but is always cleared.
Instructions where the PCL is the destination, or Modify PCL instructions, include MOVWF PC, ADDWF PC, and BSF PC,5.
The Program Counter is set upon a RESET, which means that the PC addresses the last location in the last page i.e., the oscillator calibration instruction. After executing MOVLW XX, the PC will roll over to location 00h, and begin executing user code.
The STATUS register page preselect bits are cleared upon a RESET, which means that page 0 is pre-selected.
Therefore, upon a RESET, a GOTO instruction will automatically cause the program to jump to page 0 until the value of the page bits is altered. PIC12C5XX devices have a 12-bit wide L.I.F.O. hardware push/pop stack to Attack IC PIC16C74B Binary.
A CALL instruction will push the current value of stack 1 into stack 2 and then push the current program counter value, incremented by one, into stack level 1. If more than two sequential CALL’s are executed, only the most recent two return addresses are stored when Recover Chip PIC12CE518 Binary.
ARETLW instruction will pop the contents of stack level 1 into the program counter and then copy stack level contents into level 1. If more than two sequential RETLW’s are executed, the stack will be filled with the address previously stored in level 2. Note that the W register will be loaded with the literal value specified in the instruction. This is particularly useful for the implementation of data look-up tables within the program memory when MCU Cracking.
Upon any reset, the contents of the stack remain unchanged, however the program counter (PCL) will also be reset.