 Break ATmel Locked Chip ATmega1281V Program
Break ATmel Locked Chip ATmega1281V Program
We can break ATmel locked chip ATMEGA1281V program, please view the ATmel locked chip ATMEGA1281V features for your reference:
The device is manufactured using Atmel’s high density non-volatile memory technology. The On-chip ISP Flash allows the program memory to be reprogrammed In-System through an SPI serial interface, by a conventional non-volatile memory programmer.
Or by an On-chip Boot program running on the AVR core. The Boot program can use any interface to download the application program in the Application Flash memory.
Software in the Boot Flash section will continue to run while the Application Flash section is updated, providing true Read-While-Write operation before Break ATmel Locked Chip ATmega1281V Program.
By combining an 8-bit RISC CPU with In-System Self-Programmable Flash on a monolithic chip, the Atmel ATMEGA1281V is a powerful microcontroller that provides a highly flexible and cost effective solution to many embedded control applications.
The ATMEGA1281V AVR is supported with a full suite of program and system development tools including: C Compilers, Macro Assemblers, Program Debugger/Simulators, In-Circuit Emulators, and Evaluation kits when Break ATmel Locked Chip ATmega1281V Program.
The ATMEGA1281V differ only in memory sizes, boot loader support, and interrupt vector sizes. Table 2-1 summarizes the different memory and interrupt vector sizes for the devices.
ATMEGA1281V support a real Read-While-Write Self-Programming mechanism. There is a separate Boot Loader Section, and the SPM instruction can only execute from there.
In ATMEGA1281V there is no Read-While-Write support and no separate Boot Loader Section. The SPM instruction can execute from the entire Flash after Break ATmel Locked Chip ATmega1281V Program.
Reliability Qualification results show that the projected data retention failure rate is much less than 1 PPM over 20 years at 85°C or 100 years at 25°C if BREAK IC.
 Decrypt Encrypted Atmel Chip ATmega2561 Source Code
Decrypt Encrypted Atmel Chip ATmega2561 Source Code
We can decrypt encrypted Atmel Chip ATMEGA2561 source code, please view the encrypted Atmel Chip ATMEGA2561 features for your reference:
This documentation contains simple code examples that briefly show how to use various parts of the device. These code examples assume that the part specific header file is included before compilation. Be aware that not all C compiler vendors include bit definitions in the header files and interrupt handling in C is compiler dependent.
Please confirm with the C compiler documentation for more details. For I/O Registers located in extended I/O map, “IN”, “OUT”, “SBIS”, “SBIC”, “CBI”, and “SBI” instructions must be replaced with instructions that allow access to extended I/O. Typically “LDS” and “STS” combined with “SBRS”, “SBRC”, “SBR”, and “CBR” before Decrypt Encrypted Atmel Chip ATmega2561 Source Code.
The Atmel® QTouch® Library provides a simple to use solution to realize touch sensitive interfaces on most Atmel AVR® microcontrollers. The QTouch Library includes support for the Atmel QTouch and Atmel QMatrix® acquisition methods.
Touch sensing can be added to any application by linking the appropriate Atmel QTouch Library for the AVR Microcontroller. This is done by using a simple set of APIs to define the touch channels and sensors, and then calling the touch sensing API’s to retrieve the channel information and determine the touch sensor states.
The QTouch Library is FREE and downloadable from the Atmel website at the following location: www.atmel.com/qtouchlibrary. For implementation details and other information, refer to the Atmel QTouch Library User Guide – also available for download from Atmel website if Decrypt Encrypted Atmel Chip ATmega2561 Source Code.
1. For compatibility with future devices, reserved bits should be written to zero if accessed. Reserved I/O memory addresses should never be written.
2. I/O Registers within the address range 0x00 – 0x1F are directly bit-accessible using the SBI and CBI instructions. In these registers, the value of single bits can be checked by using the SBIS and SBIC instructions.
3. Some of the Status Flags are cleared by writing a logical one to them. Note that, unlike most other AVRs, the CBI and SBI instructions will only operate on the specified bit, and can therefore be used on registers containing such Status Flags when Decrypt Encrypted Atmel Chip ATmega2561 Source Code.
The CBI and SBI instructions work with registers 0x00 to 0x1F only.
4. When using the I/O specific commands IN and OUT, the I/O addresses 0x00 – 0x3F must be used. When addressing I/O Registers as data space using LD and ST instructions, 0x20 must be added to these addresses.
The ATMEGA2561 is a complex microcontroller with more peripheral units than can be supported within the 64 location reserved in Opcode for the IN and OUT instructions.
For the Extended I/O space from 0x60 – 0xFF in SRAM, only the ST/STS/STD and LD/LDS/LDD instructions can be used.
5. Only valid for ATMEGA2561 when RECOVER MCU.
6. BODS and BODSE only available for picoPower devices ATMEGA2561
 Attack Atmel Chip ATmega2561V Secure Code
Attack Atmel Chip ATmega2561V Secure Code
We can attack Atmel Chip ATMEGA2561V secure code, please view the Atmel Chip ATMEGA2561V features for your reference:
· Analog MUX can be turned off when setting ACME bit
· TWI Data setup time can be too short
1. Analog MUX can be turned off when setting ACME bit
If the ACME (Analog Comparator Multiplexer Enabled) bit in ADCSRB is set while MUX3 in ADMUX is ‘1’ (ADMUX[3:0]=1xxx), all MUX’es are turned off until the ACME bit is cleared.
Problem Fix/Workaround
Clear the MUX3 bit before setting the ACME bit.
2. TWI Data setup time can be too short
When running the device as a TWI slave with a system clock above 2MHz, the data setup time for the first bit after ACK may in some cases be too short. This may cause a false start or stop condition on the TWI line before Attack Atmel Chip ATmega2561V Secure Code.
Problem Fix/Workaround
Insert a delay between setting TWDR and TWCR.
· Analog MUX can be turned off when setting ACME bit
· TWI Data setup time can be too short
Typical values contained in this data sheet are based on simulations and characterization of other AVR Atmel Chips manufactured on the same process technology when Attack Atmel Chip ATmega2561V Secure Code.
Min and Max values will be available after the device is characterized. The ATmega64 is a low-power CMOS 8-bit Atmel Chip based on the AVR enhanced RISC architecture.
By executing powerful instructions in a single clock cycle, the ATmega64 achieves throughputs approaching 1 MIPS per MHz, allowing the system designer to optimize power consumption versus processing speed.
The AVR core combines a rich instruction set with 32 general purpose working registers.
All the 32 registers are directly connected to the Arithmetic Logic Unit (ALU), allowing two independent registers to be accessed in one single instruction executed in one clock cycle before BREAK IC.
The resulting architecture is more code efficient while achieving throughputs up to ten times faster than conventional CISC Atmel Chips.
 Reverse Engineering Atmel MCU ATtiny48 Heximal
Reverse Engineering Atmel MCU ATtiny48 Heximal
We can reverse engineering Atmel MCU ATTINY48 heximal, please view the Atmel MCU ATTINY48 features for your reference:
· High-performance, Low-power AVR® 8-bit Atmel MCU
· Advanced RISC Architecture
– 90 Powerful Instructions – Most Single Clock Cycle Execution
– 32 x 8 General Purpose Working Registers
– Fully Static Operation
Nonvolatile Program and Data Memories
– 1K Byte In-System Programmable Flash Program Memory
Endurance: 1,000 Write/Erase Cycles
– 64 Bytes EEPROM
Endurance: 100,000 Write/Erase Cycles
– Programming Lock for Flash Program Data Security before Reverse Engineering Atmel MCU ATtiny48 Heximal
Peripheral Features
– Interrupt and Wake-up on Pin Change
– Two 8-bit Timer/Counters with Separate Prescalers
– One 150 kHz, 8-bit High-speed PWM Output
– 4-channel 10-bit ADC
One Differential Voltage Input with Optional Gain of 20x
– On-chip Analog Comparator
– Programmable Watchdog Timer with On-chip Oscillator
Special Atmel MCU Features
– In-System Programmable via SPI Port
– Enhanced Power-on Reset Circuit
– Programmable Brown-out Detection Circuit if Reverse Engineering Atmel MCU ATtiny48 Heximal
– Internal, Calibrated 1.6 MHz Tunable Oscillator
– Internal 25.6 MHz Clock Generator for Timer/Counter
– External and Internal Interrupt Sources
– Low-power Idle and Power-down Modes
Power Consumption at 1.6 MHz, 3V, 25°C
– Active: 3.0 mA
– Idle Mode: 1.0 mA
– Power-down: < 1 µA
I/O and Packages
– 8-lead PDIP and 8-lead SOIC: 6 Programmable I/O Lines
Operating Voltages
– 2.7V – 5.5V
Internal 1.6 MHz System Clock
The ATtiny15L is a low-power CMOS 8-bit Atmel MCU based on the AVR RISC architecture if reverse engineering microcontroller.
By executing powerful instructions in a single clock cycle, the ATTINY48 achieves throughputs approaching 1 MIPS per MHz allowing the system designer to optimize power consumption versus processing speed.
 Recovery IC ATtiny48V Encrypted Firmware
Recovery IC ATtiny48V Encrypted Firmware
We can recovery IC ATTINY48V encrypted firmware, please view the IC ATTINY48V features for your reference:
The AVR core combines a rich instruction set with 32 general purpose working registers.
All the 32 registers are directly connected to the Arithmetic Logic Unit (ALU), allowing two independent registers to be accessed in one single instruction executed in one clock cycle.
The resulting architecture is more code efficient while achieving throughputs up to ten times faster than conventional CISC microcontrollers.
The ATTINY48V provides 1K byte of Flash, 64 bytes EEPROM, six general purpose I/O lines, 32 general purpose working registers, two 8-bit Timer/Counters, one with high speed PWM output, internal oscillators, internal and external interrupts, programmable Watchdog Timer after Recovery IC ATtiny48V Encrypted Firmware.
4-channel 10-bit Analog-to-Digital Converter with one differential voltage input with optional 20x gain, and three software-selectable Power-saving modes.
The Idle mode stops the CPU while allowing the ADC, analog comparator, Timer/Counters and interrupt system to continue functioning.
The ADC Noise Reduction mode facilitates high-accuracy ADC measurements by stopping the CPU while allowing the ADC to continue functioning when Recovery IC ATtiny48V Encrypted Firmware.
The Power-down mode saves the register contents but freezes the oscillators, disabling all other chip functions until the next interrupt or hardware reset.
The wake-up or interrupt on pin change features enable the ATtiny48V to be highly responsive to external events, still featuring the lowest power consumption while in the Power-saving modes.
The device is manufactured using Atmel’s high-density, nonvolatile memory technology. By combining a RISC 8-bit CPU with Flash on a monolithic chip, the ATtiny15L is a powerful microcontroller that provides a highly flexible and cost-efficient solution to many embedded control applications when Recovery IC ATtiny48V Encrypted Firmware.
The peripheral features make the ATTINY48V particularly suited for battery chargers, lighting ballasts and all kinds of intelligent sensor applications.
The ATTINY48V AVR is supported with a full suite of encrypted firmware and system development tools including macro assemblers, encrypted firmware debugger/simulators, In-circuit emulators and evaluation kits after Recover MCU.
 Decrypt Encrypted Microcontroller ATmega16PA Code
Decrypt Encrypted Microcontroller ATmega16PA Code
We can Decrypt Encrypted Microcontroller ATmega16PA Code, please view the Encrypted Microcontroller ATmega16PA features for your reference:
Port B is a 6-bit I/O port. PB4..0 are I/O pins that can provide internal pull-ups (selected for each bit). PB5 is input or open-drain output.
The use of pin PB5 is defined by a fuse and the special function associated with this pin is external Reset. The port pins are tristated when a reset condition becomes active, even if the clock is not running if decrypt encrypted microcontroller.
The internal oscillator provides a clock rate of nominally 1.6 MHz for the system clock (CK). Due to large initial variation (0.8 -1.6 MHz) of the internal oscillator, a tuning capability is built in.
Through an 8-bit control register – OSCCAL – the system clock rate can be tuned with less than 1% steps of the nominal clock after decrypt encrypted microcontroller.
There is an internal PLL that provides a 16x clock rate locked to the system clock (CK) for the use of the Peripheral Timer/Counter1. The nominal frequency of this peripheral clock, PCK, is 25.6 MHz.
The fast-access register file concept contains 32 x 8-bit general purpose working registers with a single-clock-cycle access time. This means that during one single clock cycle, one ALU (Arithmetic Logic Unit) operation is executed if decrypt encrypted microcontroller.
Two operands are output from the register file, the operation is executed, and the result is stored back in the register file – in one clock cycle.
Two of the 32 registers can be used as a 16-bit pointer for indirect memory access. This pointer is called the Z-pointer, and can address the register file, IO file and the code program memory before decrypt encrypted microcontroller.
The ALU supports arithmetic and logic functions between registers or between a constant and a register. Single-register operations are also executed in the ALU.
Figure 2 shows the ATtiny15L AVR RISC microcontroller architecture. The AVR uses a Harvard architecture concept with separate memories and buses for program and data memories.
The program memory is accessed with a two-stage pipeline. While one instruction is being executed, the next instruction is pre-fetched from the program memory.
This concept enables instructions to be executed in every clock cycle. The program memory is In-System Programmable code memory if Reverse Engineering Microcontroller.
 Break Protected Microcontroller ATmega164 Locked Flash
Break Protected Microcontroller ATmega164 Locked Flash
We can break Protected Microcontroller ATMEGA164 locked flash, please view Protected Microcontroller ATMEGA164 features for your reference:
The BOD circuit will only detect a drop in VCC if the voltage stays below the trigger level for longer than 3 µs for trigger level 4.0V, 7 µs for trigger level 2.7V (typical values).
When the Watchdog times out, it will generate a short reset pulse of 1 CK cycle duration. On the falling edge of this pulse, the delay timer starts counting the time-out period tTOUT. Refer to page 34 for details on operation of the Watchdog Timer if Break Protected Microcontroller ATmega164 Locked Flash.
To make use of the reset flags to identify a reset condition, the user should read and then reset the MCUSR as early as possible in the program.
If the register is cleared before another reset occurs, the source of the reset can be found by examining the reset flags. ATmega164 features an internal bandgap reference with a nominal voltage of 1.22V after Break Protected Microcontroller ATmega164 Locked Flash.
This reference is used for Brown-out Detection, and it can be used as an input to the Analog Comparator. The 2.56V reference to the ADC is generated from the internal bandgap reference.
The voltage reference has a start-up time that may influence the way it should be used. The maximum start-up time is TBD. To save power, the reference is not always turned on. The reference is on during the following situations:
1. When the BOD is enabled (by programming the BODEN fuse).
2. When the bandgap reference is connected to the Analog Comparator (by setting the AINBG bit in ACSR).
3. When the ADC is enabled before BREAK IC.
 CPLD Crack Method Description
CPLD Crack Method Description
CPLD Crack Method Description refers to describe the way to crack CPLD chip protection system and readout firmware from memory cells;
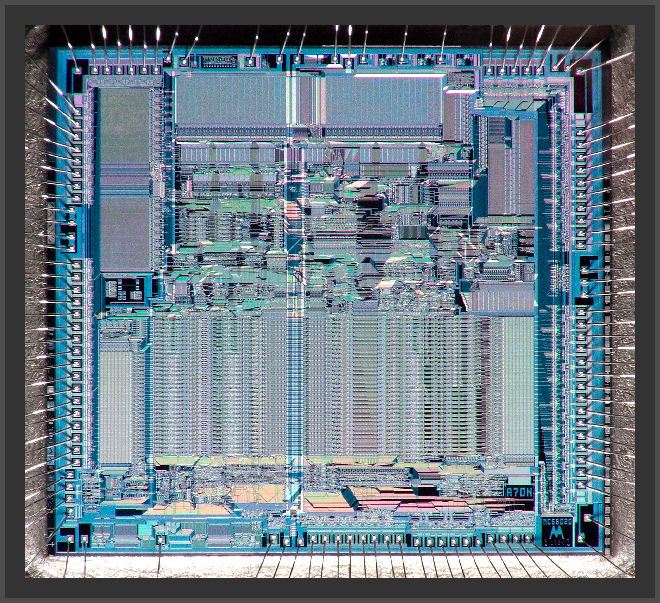
The principle of this technology is exposure internal wire connection, through inspection, manipulation and interfere MCU to achieve CPLD chip program information purpose.
For more convenience, people can separate above 4 methods into 2 categories: 1 is intruded cpld attacking encrypted code, this kind of crack will need to decap the package, and then by the assistance of semiconductor testing device, microscope and mini-locator, spend several hours or even weeks can finish in a dedicated lab.
All the probe technology can be classified as intruded cpld crack. The other 3 ways belong to un-intruded crack, objects wouldn’t be damaged physically. In some occasion un-intruded CPLD ic source code attacking is very dangerous, that is because un-intruded device can be self-made and upgrade, cost is very low.
A majority of un-intrude cpld need hacker have good knowledge of microprocessor and software. On the contrary, intruded probe cpld mcu ic hack don’t need too much knowledge, moreover can use a set of similar technology to deal with products in wider scope. As a result of that, CPLD hacking normally start from intruded IC crack, accumulated experience will help you develop more economical and faster un-intruded crack technology.
 FPGA Crack method
FPGA Crack method
FPGA crack’s Error-Occurring technology
Through abnormal operation situation to let errors occur in FPGA, and then provide extra accessing to crack FPGA, the most commonly used error-occurring methods include voltage shock and clock shock, low voltage and high voltage fpga crack can be applied for prohibition of circuit protection or force microprocessor to operate errors. Clock transient hop maybe can re-set circuit protection but won’t damage protected information. Power supply and clock transient hop can affect recovery and execution of single order in part of FPGA.
 How to Extract MCU Code
How to Extract MCU Code
How to Extract MCU Code is a task for engineers who wants to make IC clone from exisiting microcontroller memory reading;
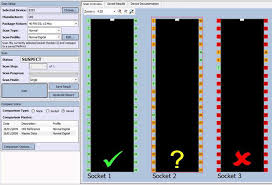
The principle of this method is monitor simulation characteristic of all the power supply and interface connection during the standard operation under high resolution, and copy MCU firmware by monitoring its electromagnetic radiation.
Because MCU is an active electronic component, when it operate different orders, corresponding power supply consumption will alter accordingly. Then use special electronic measurement device and mathematic statistical method to analyze and detect these changes, can extract code embedded inside microprocessor.
Currently RF programmer can read program of old MCU is base upon this principle.