The outcome of ignorance in understanding the Microcontroller Breaking directions could be devastating to many modern devices going online or wireless as part of the Internet-of-Things (IoT) initiative. Modern semiconductors which have wireless connectivity could be cracked in many ways through software vulnerabilities and backdoors.
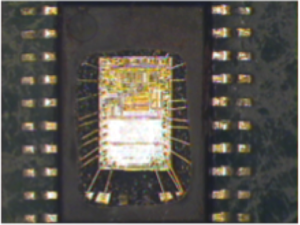
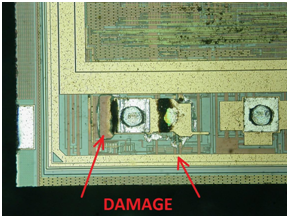
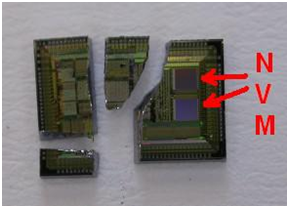
Sometime the research could even lead to impossible achievements. This happens when someone senior tells that certain things are not possible, but the research proves them wrong. This could result in a large outcry in the media like it was in the case of NAND mirroring attack on iPhone 5C [9]. There are some impossible challenges faced by Forensic Analysis engineers, for example, MCU data extraction from electrically damaged (Fig. 1) and mechanically damaged (Fig.2).
Although the contents of the on-chip non-volatile memory was fully preserved, conventional Failure Analysis methods are not only very expensive but would also require weeks or months of tedious work. However, it is very likely that Hardware Security would be able to come up with feasible and affordable solutions in the nearest future.
As a contribution to the wide list of already known MCU memory breaking this paper introduces two new attacks. One is about efficient microprobing of an old smartcard chip, another is about decapsulation of a microcontroller with battery-backed on-chip SRAM.